Set of 15 flat internet security and icons - Trojan, traffic encryption, remote support, Sql, Router, Secure Payment, Scan, Remote access. Vector illustration isolated on colorful background Stock Vector | Adobe Stock
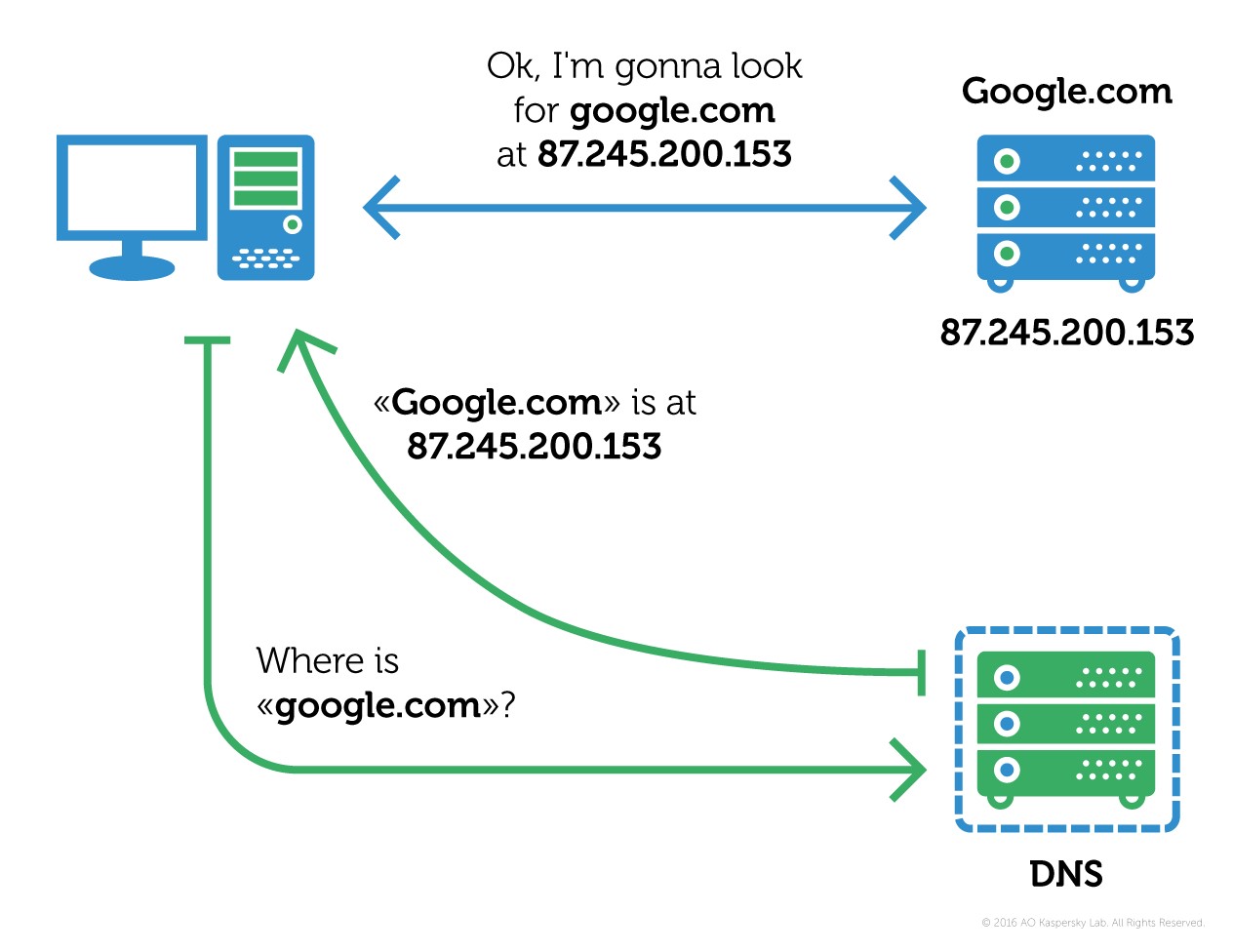
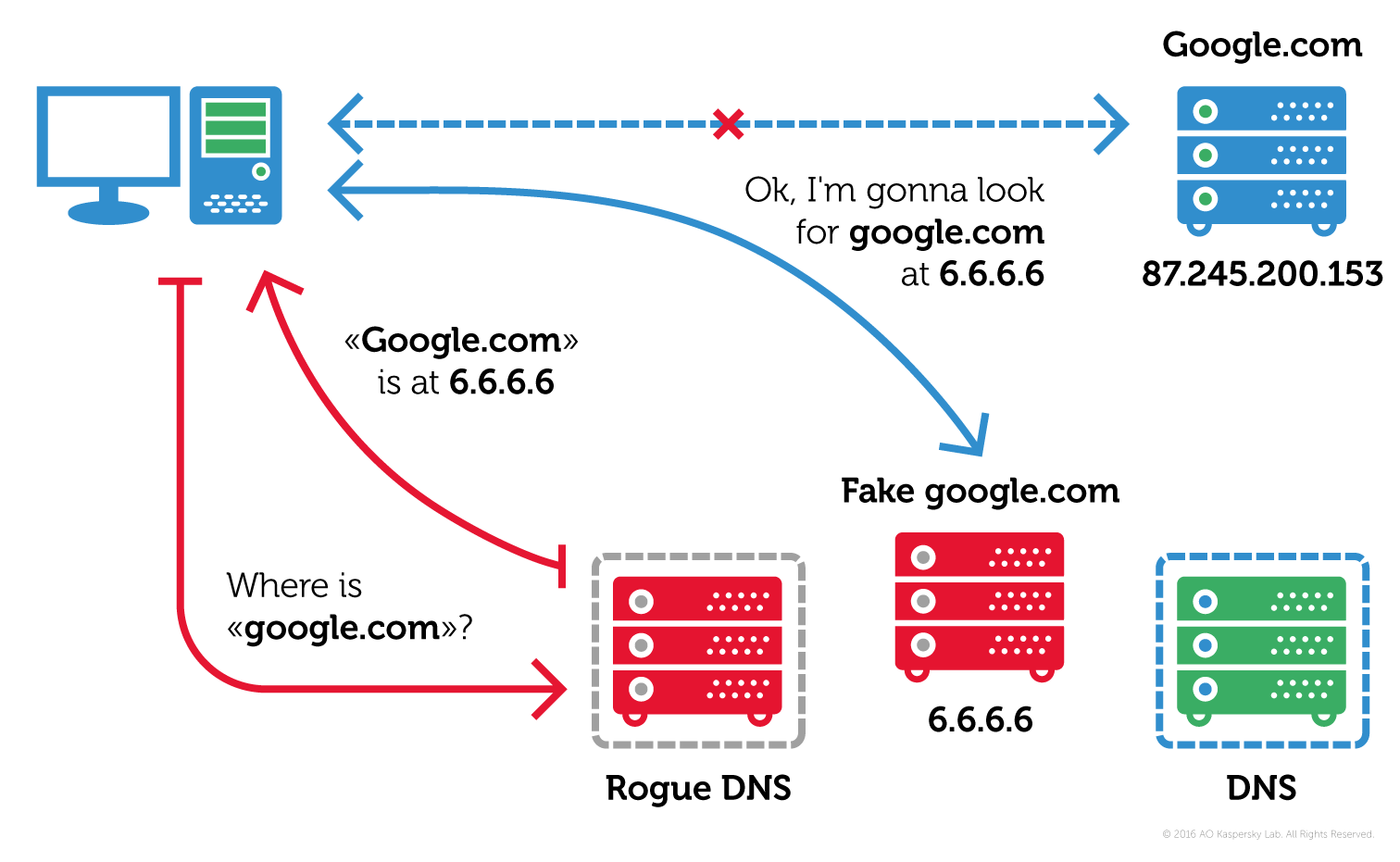
A new multistage remote access trojan ZuoRAT has been targeting SOHO routers in North America and Europe

Your WiFi Router is Not SAFE: Chinese State-Sponsored Malware Turns Innocent Routers into Cyber Spies | Technology & Science News, Times Now



:max_bytes(150000):strip_icc()/can-a-router-get-a-virus-4768395-11-247068e0211549a8991da4f3b3353f1c.png)